The practice of transferring and storing information securely by specific form is known as cryptography. It allows only authorized users to access the data through strong authentication. By this page, you can acquire more info on interesting research developments in cryptography project ideas from the latest research areas!!!
What are the key terms in cryptography?
The two key terms used in cryptography are plaintext and ciphertext. By the by, the plain text refers to human-readable text, and ciphertext refers to human unreadable text. The process of converting plain text into ciphertext is called encryption and the process of converting ciphertext into plain text is called decryption. There are some special kinds of cryptographic techniques such as Hash function, Asymmetric (public-key), and Symmetric (private-key) cryptography.
What is cryptography and how it works?
The main aim of cryptography is to give complete security over communication even there is a threat of malicious attacks/adversaries. On the sender side, the sender applies an encryption algorithm to form ciphertext from original plain text. Then, pass the encoded data with a key to the receiver. On the receiver side, the receiver applies a decryption algorithm using a key to get back original plain text from the ciphertext.
In this way, cryptographic technique assures security and integrity over transferring data even in presence of malicious attacks/adversaries. Cryptographic techniques are used to ensure the secrecy and integrity of data in the presence of an adversary. Generally, cryptography provides a huge number of algorithms for data transferring and storing in communication. Based on threat-level and security requirements, one should choose appropriate security schemes from cryptography.
“Cryptography is a typical method to encrypt system/network data by transforming plain text into cipher text for secure data transmission”.
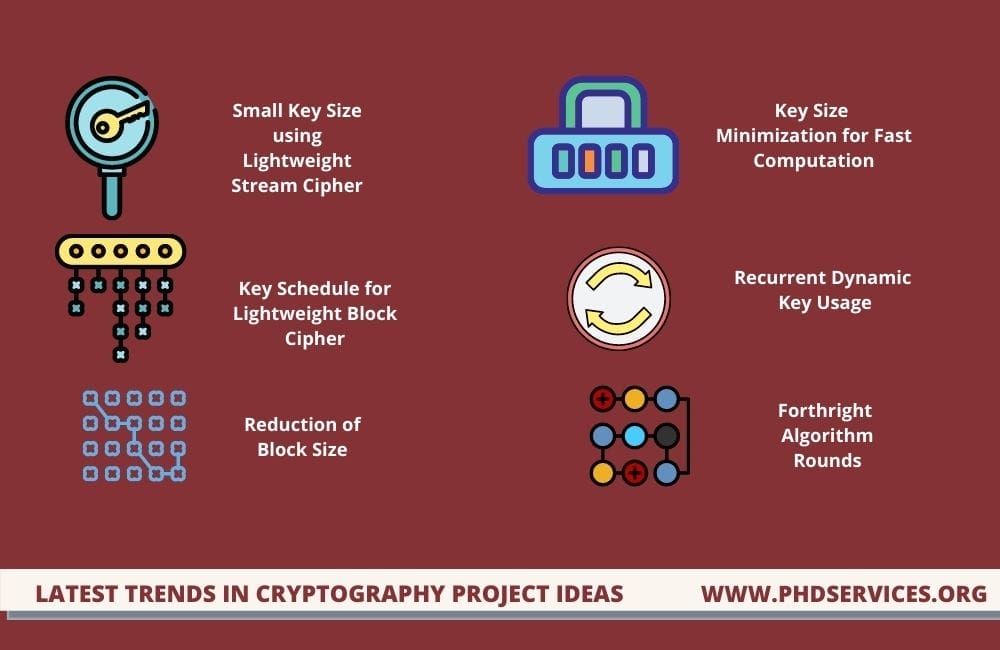
Current Trends in Cryptography Project Ideas
- Vector Initialization, Internal state, Small Key Size using Lightweight Stream Cipher
- New Key Schedule for Lightweight Block Cipher
- Key Size Minimization for Fast Computation
- Reduction of Block Size
- Enhancing Recurrent Dynamic Key Usage
- Generating more Forthright Algorithm Rounds
Further, we have also given you creative cryptography project topics from top-trending research areas of cryptography. These lists of project topics are guaranteed to achieve cryptography objectives as fullest security over communication data
Now, we can see the need for cryptographic techniques in data communication. Currently, large-scale systems are connected to transfer information. Cryptography is nothing but security technology to protect data from attackers and hackers while transmission. For that, it focuses on data integrity, data privacy, and user/network device authentication.
What is the purpose of cryptography?
- Data Integrity
- Transmission data should not be changed by unauthenticated users
- Privacy
- Transmitted data is needed to be known only by authenticated users
- Authentication
- Verifying the real identity of sender and receiver before communication
Next, we can see about technical obstacles faced by cryptography to attain security over data communication. There are numerous research issues in implementing cryptographic techniques. For your information, here we have given only two main problems. Our developers have computed different solutions to solve these problems.
To know the apt solutions for these problems, contact us. We let you know solutions along with other emerging research problems in cryptography. We assure you that our proposed research techniques are robust in security to implement novel cryptography project ideas.
What is the big problem in cryptography?
- Lack of strong mathematical strength in authentication and key management over large-scale environ
- Current algorithms may be less-effective to handle new developments in numerical computation
In addition, we have given you the list of key factors that increase the robustness of the cryptographic techniques and algorithms. On proposing suitable research solutions for your selected research problems, we consider all these default factors to acquire expected system performance.
From our long-term experience, our developers also know different smart approaches to improve the robustness of algorithms. Based on your project requirements, we suggest appropriate cryptographic techniques.
How to compute the strength of cryptography?
- Delay
- Key size
- Gated area
- Block length
- Throughput
- Total count of rounds
Similar to factors for strengthening cryptographic techniques, some elements help you to choose optimal cryptographic algorithms. Since good cryptographic technique only determines your project performance and efficiency. Also, it only makes your proposed research work unique from others. We provide you with current trends along with innovative Cryptography Project Ideas. So, it is necessary to consider all these elements along with project objectives while cryptographic algorithms selections. Our developers are intelligent to choose the best-fitting techniques and algorithms for specific research issues.
How do choose the best cryptography algorithms?
- Cost
- Although serial architecture is low cost to deploy, it degrades efficiency through the added loop
- The use of small key length makes fewer memory needs and register needs
- Performance
- More number of parallel computation results in high performance/efficiency
- Less number of rounds results in low delay
- Security
- Prefer a greater number of rounds to improve cipher security
- The use of big key size decrease the time to attack
- Other Important Elements
- Assurance of accessibility
- Fault-tolerant and flaw-less design
- Make sure to have enough key size to overcome the security issues
- Regular updatable cryptographic modules
- Avoid high-computational algorithm that has high-complexity overhead
- Presence of authentication alternatives to overcome connectivity issue
To make you aware of important cryptographic algorithms, here we have prepared this list of algorithms. Each algorithm has different characteristics to perform the programmed task. Therefore, one should know the purpose of each algorithm before preferring for your research problems. As well, all our ideas are collected by analyzing the current research direction of cryptography. In any case, if you are interested to know other emerging trends over cryptography project ideas then create a bond with us.
Our developers have more than enough experience in practicing these algorithms on various cryptography projects. Beyond this list, we also serve on other significant cryptographic algorithms. Further, we are also good at developing hybrid techniques to tackle complicated research issues.
Important Cryptography Algorithms
- Asymmetric Algorithms
- ECC
- RSA
- XTR
- Diffie Hellman
- Symmetric Algorithms
- CAST
- Twofish and Blowfish
- IDEA
- RC2, RC4, and RC6
- E-DES, T-DES, 3-DES and DES
- AES
For illustration purposes, here we have selected E-DES, AES, 3DES, and DES algorithms as examples from the above list. In this, we have compared the characteristics/properties of all three algorithms for your reference. Likewise, you have to analyze all your possible solutions (techniques) to choose the optimum one among them.
By performing this comparative study in your project development, you can gain accurate results and high performance in project execution. Further, if you are curious to know about other cryptographic algorithms then approach our development team.
Comparison Analysis of Cryptography Algorithms
- E-DES
- Block Size (bits) – 128
- Key Size (bits) – 1024
- Cipher Type – Symmetric
- Rounds – 16
- Possible Key – 21024
- Encode Software – Ultra-Speed
- Encode Duration – 2 sec
- BF Key Attack Duration – 10152 years
- Avalanche Impact – Resists
- AES
- Block Size (bits) – 128
- Key Size (bits) – 256, 128, 192
- Cipher Type – Symmetric
- Rounds – 14, 10, 12
- Possible Key – 2128
- Encode Software – Moderate
- Encode Duration – 13 sec
- BF Key Attack Duration – l029years
- Avalanche Impact – Resists
- 3DES
- Block Size (bits) – 64
- Key Size (bits) – 168, 112
- Cipher Type – Symmetric
- Rounds – 48
- Possible Key – 2112
- Encode Software – Slow
- Encode Duration – 21 sec
- BF Key Attack Duration – 1.6 x 1014 years
- Avalanche Impact – Resists
- DES
- Block Size (bits) – 64
- Key Size (bits) – 56
- Cipher Type – Symmetric
- Rounds – 16
- Possible Key – 216
- Encode Software – Speed
- Encode Duration – 7sec
- BF Key Attack Duration – less than 1 day
- Avalanche Impact – Resists
Additionally, we can see constraints in assessing cryptographic algorithms for general cryptography projects. These constraints are simple to solve using modern technologies of cryptography. As well, we have appropriate solutions for all these constraints. Once you connect with us, we share those solutions with you for sure.
Limitations of Cryptography Algorithms
- Non-equivalence of Hardware
- In general, the efficiency of the proposed system is evaluated through experimental results or values
- Conventional methods evaluate the efficiency by applying the proposed system on various hardware that have similar features
- This conventional method is complex and high in computation cost
- So, it is required to be evaluated using a single system for all algorithms
- Investigation of Informal Security
- Based on formal and informal security inspection, the efficiency of findings can be evaluated
- Formal analysis of proposed algorithms needs to follow the same evaluation tool and techniques
- So, it helps to identify probable vulnerabilities in a proposed system with an accurate report
Although different lightweight cipher algorithms are developed, they are not effective to achieve low energy usage, small chip area, high security, low power usage, low delay, etc. We have several unique cryptography project ideas for overcoming these challenges. Here, we have classified the challenges into lightweight stream cipher and lightweight block cipher. We ensure you that our proposed techniques are enhanced in several aspects like accuracy, security, fast computation, etc.
Lightweight Cryptography Challenges
- Lightweight Stream Cipher Challenges
- Minimize chip area
- Implement smallest key length
- Reduce internal state
- Lightweight Block Cipher challenges
- Constantly use dynamic key
- Apply lowest key length
- Design easy key structure
- Produce a smaller number of algorithm rounds
- Implement tiny unit of data (i.e., block)
Next, we can see about latest trends in developing cryptography project ideas. Majorly, all these project ideas are underlying significant research issues of cryptography. More than these ideas, we also extend our service to trending technologies of cryptography like quantum cryptography.
To give you unique project ideas, we have referred to several current cryptography research papers. In this, we have examined all possible security attacks, threats, and vulnerabilities along with existing solving techniques. This makes us think out-of-the-box for accomplishing advanced project topics.
Innovative Top 15+ Interesting Cryptography Project Ideas
- Security over Mobile Communication
- Enhanced Security Threat Analysis
- Cybersecurity based on Applied Cryptography
- Secure Fog-Cloud and Fog-Edge Computing
- Intrusion Detection and Prevention Systems
- ML Techniques for Cryptography and Cybersecurity
- Hardware Trojans Identification and Stoppage
- Resilience Challenges in Cyber-Physical Systems
- Web-based Malware Detection, Analysis, and Prevention
- Privacy, Trust and Security in Cloud Computing Hardware
- Possible Computer Fault Attacks and Preventive Measures
- Security Attack Detection and Mitigation in Side-channel
- Cybersecurity against Cyber-attacks in the Internet of Things
- Advanced Detection of Denial-of-Service (DoS) Attacks
- Advance Security Mechanism for Artificial Intelligence
- Efficient Security Threats, Attacks and Vulnerabilities Analysis
- Standardized Techniques for Hardware and Software Security
To the end, we can see about the performance evaluation phase of cryptography projects. Once you complete the development and execution of your project, you have to assess the performance of the proposed cryptography algorithms.
This process helps you to inspect the efficiency of your research work from other previous techniques. For your knowledge, here we have given you two primary metrics in analyzing cryptographic algorithms.
Performance Analysis of Cryptography Algorithms
- Communication cost
- Measures the overall transmitted message size while communication
- Computation cost:
- Measures the overall execution time of proposed techniques
In specific, combine the execution time of all operations involved in the cryptographic scheme and compute the overall sum as computation cost. When the data is transmitted between sender and receiver, several operations and transactions are influenced by scheme design. Similarly, there are performance metrics to assess proposed methodologies’ performance.
Overall, we have a massive amount of Cryptography Project Ideas from different perceptions of research. We assure you that our suggested ideas are unique in creating your contribution to social developments. When you selected your inspired project topic from our collections, we recommend suitable development tools and technologies. Then, we give a well-organized implementation plan with apt performance evaluation metrics for your selected project. Next, we implement your selected project on your confirmed development platform and programming language. At last, we deliver your project with assured results on time.



















