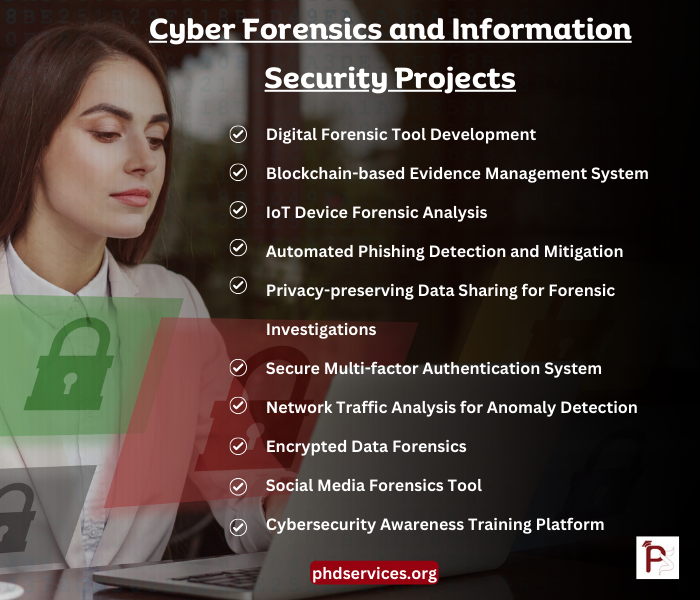
Generally, cybersecurity is the most significant area that contains different subdomains in it. Cyber Forensics and Information Security Projects are trending in recent days we carry out perfect ccomparative analysis by examining the trending papers of that current year. Reference papers that we used for your research work will be shared. Hurry up contact us to score high grade. The following are various project strategies which range cyber forensics as well as the information security for beginners, researchers and students to support these challenging fields:
- Privacy-preserving Data Sharing for Forensic Investigations
- Project Plan: To allow the distribution of data between law enforcement corporations for forensic research without convincing the confidentiality of users, discover and incorporate privacy-preserving technologies like safe multi-party computation or homomorphic encoding.
- Digital Forensic Tool Development
- Project Plan: It concentrates on improving precision, acceleration and user interface. To automate the task of gathering, observing and documenting smart proof from several sources like cloud storage, mobile devices and hard drives, create and utilize the smart forensic equipment.
- Blockchain-based Evidence Management System
- Project Plan: From gathering up to courtroom demonstration, handle digital proof by assuring its reliability, non-deniability and morality and develop a blockchain-oriented environment. In virtual explorations, this model can solve chain-of-custody problems which are typical.
- Network Traffic Analysis for Anomaly Detection
- Project Plan: To find abnormalities signaling cyber threats or illicit behaviors, apply a model which observes network traffic practically. According to the traffic designs, increase identification precision by using machine learning methods.
- IoT Device Forensic Analysis
- Project Plan: Aim at forensic observation technologies for IoT devices and organize a research assignment. For data retrieving and observation from digital home appliances, automotive mechanisms and wearables, examine the specific problems which are introduced by them. This strategy also includes developing methods regarding that.
- Secure Cloud Computing Architecture
- Project Plan: Solve the major protection issues like access control, safe data distribution between cloud services and data security through creating a safe framework for cloud computing platforms.
- Secure Multi-factor Authentication System
- Project Plan: For improving protection for online environments, develop a secure multi-factor verification structure which integrates anything the user is biometric checking, the aspect the user has such as mobile device or safety token and something the user knows like password.
- Automated Phishing Detection and Mitigation
- Project Plan: To identify phishing emails or websites practically and take suitable reduction measures in an automatic way like blocking unwanted contents and notifying users, this designs an AI-oriented structure. On legitimate emails or web pages and phishing dataset, instruct the model with the help of machine learning.
- Encrypted Data Forensics
- Project Plan: By targeting methods such as consent-related usage, cryptographic key recovery and side-channel threats, investigate techniques and design tools for forensic observation of encoded data without decoding.
- Cybersecurity Awareness Training Platform
- Project Plan: For teaching the users in terms of general attacks such as phishing, malware and social engineering, the process of securing private and associational data, and great experiences on cybersecurity, it is necessary to create a communicative, enthusiastic training environment based on the web.
- Malware Analysis and Classification Framework
- Project Plan: According to their activity, influence and features, construct a model for observing and categorizing malware samples. To detect unknown malware factors and automate the categorization task, include the machine learning methods.
- Social Media Forensics Tool
- Project Plan: To assist valid explorations or cybersecurity events in the forensic research of social media, design a tool which has the ability of gathering, protecting and observing data from different social media environments.
Could anybody suggest few topics in digital forensics for a final project?
According to security related fields, digital forensics is a rapidly evolving area which contains different types of topics that meet the advanced technologies. We offer a list of various topics that are applicable for an effective final project which has several features of digital forensics:
- Forensic Analysis of Cloud Storage Services
- By determining the multi-tenancy platform and data dispersion throughout world-wide data centers in cloud services such as Google Cloud, Microsoft Azure, and AWS, explore the difficulties and technologies for organizing forensic observation on stored data.
- IoT Device Forensics
- Concentrating on the retrieval and observation of data from digital home devices, automotive mechanisms, specific difficulties were they involved and digital home devices and researching the forensic research of IoT devices.
- Machine Learning Techniques in Digital Forensics
- To automate the analysis of virtual proof like detecting figures in huge datasets of digital interactions or forecasting the kind of offense in terms of smart artifacts, design a machine learning-oriented framework or device.
- Blockchain and Digital Forensics
- For forensic research that includes blockchain-oriented applications, smart contracts and cryptocurrency, research the influence of blockchain technique on smart forensics along with chances and limitations.
- Mobile Forensics and App Analysis
- By determining the arising state of mobile operating mechanisms, user confidentiality protections and application encoding, retrieve and observe data from mobile devices and applications through organizing exploration on forensic algorithms.
- Digital Forensics in Cyber Incident Response
- Aiming at the protection, timely gathering and observation of proof that adhering to a cybersecurity situation, design a model or toolkit which combines smart forensic experiences into cyber incident response behaviors.
- Forensic Analysis of Encrypted Devices
- Along with the plans for avoiding or decoding locked encrypted chatting services, laptops, or smartphones, this explores the techniques for executing and observing data on encoded devices.
- Social Media Forensics
- Focusing on moral and valid restrictions and the duty of social media in advanced studies, discover forensic algorithms for gathering, protecting and recognizing data from social media settings.
- Deepfake Detection and Analysis
- Discovering the effects of deepfakes for smart proof and false-details and creating algorithms or tools to find and validate digital media by targeting the forensic observation of deepfake.
- Network Forensics and Anomaly Detection
- To detect malicious behaviors or events with the observation of network logs and the implementation of packet capture tools, develop a model or method for organizing forensic analysis on network traffic.
- Privacy-Preserving Forensics
- Through investigating approaches like secure multi-party computation or differential privacy in forensic analysis, discover techniques for organizing smart forensics research which obey user confidentiality.
- Forensic Readiness Planning
- Construct instructions or a model, especially for associations and make them manage virtual proof during, before and after a cybersecurity event in an efficient manner for improving the forensic willingness.
Cyber Forensics and Information Security Thesis Topics & Ideas
Cyber Forensics and Information Security Thesis Topics & Ideas based on current trends are shared below, we use modern methodologies and scientific method all your research ideas. Get your research paper done in perfect format from phdservices.org
- Recent developments in standards and industry solutions for cyber security and secure remote access to electrical substations
- Container Based Analysis Tool for Vulnerability Prioritization in Cyber Security Systems
- Redundancy Cyber Resiliency Technique Based on Fast ReRouting under Security Metric
- An Experimental Analysis Into Blockchain Cyber Security Attacks
- Challenges and opportunities for phasor data based event detection in transmission control centers under cyber security constraints
- Survey of Attack Projection, Prediction, and Forecasting in Cyber Security
- Cyber security components for pervasive Enterprise Security Management and the virtualization aspects
- IoT Object Authentication for Cyber Security : Securing Internet with Artificial intelligence
- Grid Cyber-Security Strategy in an Attacker-Defender Model
- Competitive Security Pricing in Cyber-Insurance Market: A Game-Theoretic Analysis
- Cyber Security Framework for Vehicular Network Based on a Hierarchical Game
- A Detailed Investigation on Various Cyber Security Models and their Comparisons with the Detailed Performance Analysis for the Application of IIOT Systems
- Instant message classification in Finnish cyber security themed free-form discussion
- Is Cyber Security Enough- A study on Big Data Security Breaches in Financial Institutions
- The Risk of Cyber Security for Power Stability Control System and Its Test Platform
- Exploiting Wireless Channel Randomness to Generate Keys for Automotive Cyber-Physical System Security
- Time Complexity of the Edge Replacement Problem in a Cyber Security System
- A Simple and Robust Approach of Random Forest for Intrusion Detection System in Cyber Security
- Demo Abstract: A HIL Emulator-Based Cyber Security Testbed for DC Microgrids
- Performance Evaluation of Shallow learning techniques and Deep Neural Network for Cyber Security


















