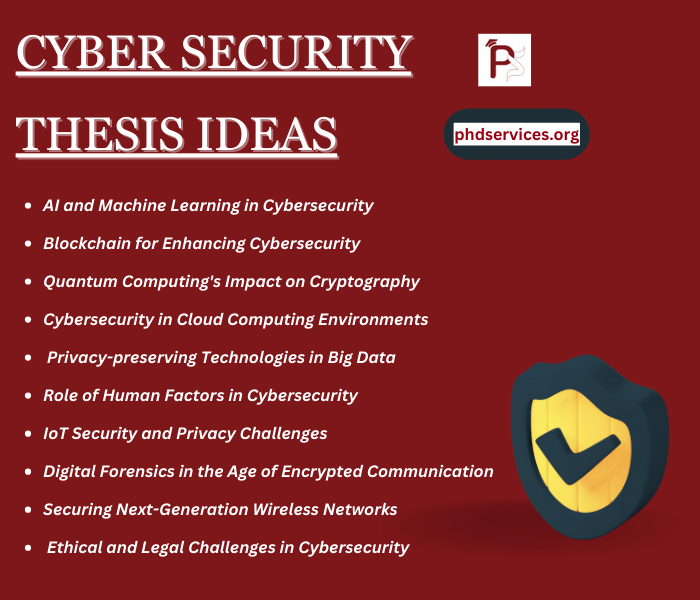
In the educational journey, thesis writing is the essential step for reflecting the scholar’s academic performance and skills. At phdservices.org, we offer a variety of Cyber Security Thesis topics for you to choose from based on your interests. We will provide you with a concise outline for your selected topic. Our well-structured work plan will guide you through the process, ensuring that all necessary content is incorporated, resulting in a flawless Cyber Security thesis. To provoke your research, we provide multiple Cyber Security Thesis Ideas among different areas in this field:
- AI and Machine Learning in Cybersecurity:
- Concept: Depending on the design in network traffic or user conduct, establish an AI-based framework to forecast and detect the cybersecurity attacks. To advance the threat prediction and time of response, this area includes practicing machine learning mechanisms on historical data of cyber-attacks.
- Blockchain for Enhancing Cybersecurity:
- Concept: In the process of protecting digital identities or securing IoT ecosystems, analyze the usage of blockchain technology. For IoT device validation and data reliability, this study intends to formulate a decentralized identity verification system or a blockchain-oriented ecosystem.
- Quantum Computing’s Impact on Cryptography:
- Concept: Examine the quantum computing effects, in what way it might impair the modern cryptographic standards and investigate the advancement of quantum-resistant techniques. A comparative study of current cryptographic techniques and their exposures to quantum attacks are included in this area.
- Cybersecurity in Cloud Computing Environments:
- Concept: As this project highlights API security, multi-tenancy and data isolation, estimate the security issues along with vulnerabilities of cloud computing. For the purpose of reducing these challenges, this study aims to develop a new security model or improvements to traditional cloud security methods.
- Privacy-preserving Technologies in Big Data:
- Concept: The capabilities of privacy-preserving technologies are considerably evaluated in securing the user information within big data programs and differential privacy or homomorphic encryption. In order to exhibit the real-time execution of these technologies, this project intends to generate a prototype.
- The Role of Human Factors in Cybersecurity:
- Concept: On the basis of managerial cybersecurity-based measures, carry out research on implications of human factors. The areas which are mainly emphasized here such as capacity of cybersecurity training programs, password usages and phishing vulnerabilities.
- IoT Security and Privacy Challenges:
- Concept: Considering the impacts of IoT (Internet of Things), analyze the specific security and secrecy issues. To assist the IoT device providers and consumers, implement productive methods or develop an extensive security system.
- Digital Forensics in the Age of Encrypted Communication:
- Concept: Regarding the period of prevalent encrypted communication, examine the confronted problems of digital forensics explorers and help them in the research process without impairing the user’s privacy by suggesting efficient techniques.
- Securing Next-Generation Wireless Networks:
- Concept: This research mainly highlights on risk which is exhibited through the novel technologies and architectures and involves the exploration of security impacts of future generation wireless networks like 5G or 6G.
- Ethical and Legal Challenges in Cybersecurity:
- Concept: Specifically in data protection principles, secrecy, and observation, evaluates the moral and legitimate problems in implementing cybersecurity procedures. Across various organisations, this study encompasses a comparative analysis of cybersecurity laws.
- Advanced Persistent Threats (APTs) and Countermeasures:
- Concept: In cyber surveillance or disruption, implement the ATP (Advanced Persistent Threats) to generate a system for earlier identification, reduction of APT operations and evaluation by means of analyzing the effective strategies or methods of APT.
- Social Engineering Attack Strategies and Defense Mechanisms:
- Concept: From common threats, secure the persons and firms by designing an extensive group of defense algorithms or training tactics through examining the psychological impact of social engineering hazards.
What is a good thesis statement for cyber security?
Thesis statement is the significant component in academic paper or thesis which presents the main essence of our research in a brief format. Across various areas of cyber security, some of the capable samples of thesis statement are suggested below:
- On the Importance of User Education:
An extensive user education program is efficiently explored in this study due to the human aspect which yet might be the vulnerable point in cyber security apart from enhanced technical securities. Among firms, this research is very important to decrease the challenges of social engineering attacks.
- Regarding Blockchain Technology:
Especially in protecting the digital transactions and IoT ecosystems, this thesis discusses the blockchain technology which provides different perspectives to improve cyber security among different fields by reason of clarity, stability and basic qualities of decentralization.
- On Quantum Computing and Cryptography:
By means of securing the next-generation digital communications from quantum attacks, this research critically examines the improvement and execution of quantum-resistant cryptographic algorithms as a consequence of vulnerable attacks which are caused by quantum computing to conventional encryption techniques.
- Concerning AI and Machine Learning in Cyber Security:
Specific requirements for ethical guidelines, effective defense algorithms in opposition to AI-based cyber-attacks and investigation of double-purpose vulnerabilities of these technologies are mainly highlighted in this subject. For generating the threat detection and response process, AI (Artificial Intelligence) and ML (Machine Learning) techniques provide unique or novel possibilities.
- Regarding IoT Security Challenges:
The advancement of regulated security measures results in critical risks because of the excessive growth of IoT devices, as this study crucially indicates. Specific problems of IoT ecosystems like user privacy, device authentication and data encryption are solved by constructing an expansive security system.
- On Privacy in the Digital Age:
This thesis significantly discusses the vital relevance of privacy-preserving technologies like homomorphic encryption or differential privacy in the period of widespread digital supervision. In the digital environment, it is important to engage in securing human rights and preserving integrity.
- Concerning Cybersecurity Policies and Governance:
To solve the complicated platform of cyber-attacks and assure durable cyber architecture, this research demands blending technology findings, global collaboration, cooperative approach and governance practices which determine the powerful cybersecurity governance.
Cyber Security Thesis Proposal Topics
phdservices.org is recognized as a highly dependable and authentic provider of Cyber Security Thesis Topics services in the research field. Our services are characterized by flexibility, excellence, and promptness, surrounding best thesis Editing and Proofreading Services, as well as thesis Writing. Our team of experienced writers possesses extensive domain knowledge, ensuring complete support in crafting your Cyber Security thesis. Additionally, we offer the flexibility to choose chapter-wise writing assistance, starting from topic selection.
- Security Requirements Analysis, Specification, Prioritization and Policy Development in Cyber-Physical Systems
- Cyber Security in Virtualized Communication Networks: Open Challenges for NATO
- Generative Adversarial Networks for Anomaly Detection in Cyber Security: A Review
- Learning From Experts’ Experience: Toward Automated Cyber Security Data Triage
- Modeling of Intrusion and Defense for Assessment of Cyber Security at Power Substations
- A Model-Based Approach for Aviation Cyber Security Risk Assessment
- Towards Unsupervised Learning based Denoising of Cyber Physical System Data to Mitigate Security Concerns
- Context Information-Based Cyber Security Defense of Protection System
- Cyber security risk assessment using an interpretable evolutionary fuzzy scoring system
- Cyber Security Intrusion Detection Using Deep Learning Approaches, Datasets, Bot-IOT Dataset
- Cyber-Physical Energy Systems Security: Threat Modeling, Risk Assessment, Resources, Metrics, and Case Studies
- SecOMN: Improved security approach for Opportunistic Mobile Networks using cyber foraging
- Cyber security threat analysis and modeling of an unmanned aerial vehicle system
- Security of Cyber Physical Systems: Vulnerabilities, Attacks and Countermeasure
- Cyber Security Analysis of DoS and MitM Attacks Against PLCs Used in Smart Grids
- Cyber-Physical Attack-Resilient Wide-Area Monitoring, Protection, and Control for the Power Grid
- Possibilities for Improving the Quality of Cyber Security Education through Application of Artificial Intelligence Methods
- A Measurement Source Authentication Methodology for Power System Cyber Security Enhancement
- Cyber security problem based on Multi-Objective Distributed Constraint Optimization technique
- A reliable security model that protects ultra-dense enterprise cloud networks from highly vulnerable cyber attacks


















