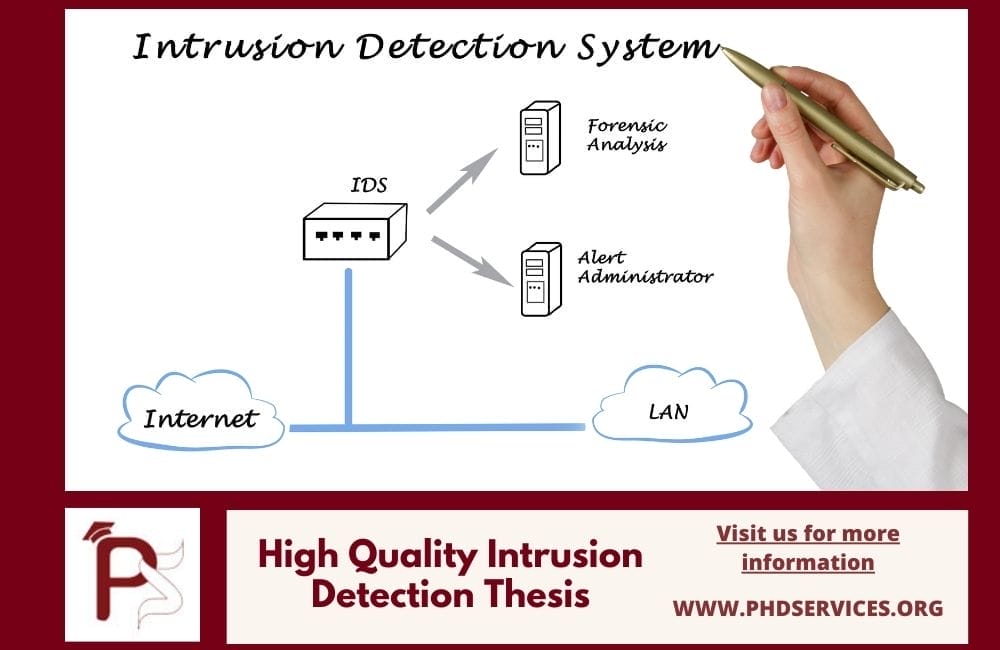
WHAT IS AN IDS? Intrusion detection system includes the hardware and software aspects of the system that are used to identify the abnormalities in a network which are the signs of intrusions (inbound and outbound). These intrusions are the result of network traffic. The intrusion detection thesis should include the major ways in which intrusions are detected and analyzed. This includes the following.
- Comparison of systems (against malware signs).
- User behavior monitoring (for detection of malicious intent).
- Harmful pattern detection by scanning processes.
- Configurations and system settings monitoring.
We give you complete research assistance for intrusion detection thesis. The following is a complete overview of the intrusion detection system research. Let us start with understanding its types.
TYPES OF IDS
There are different types of intrusion detection systems that were developed in long run by the researchers.
- Intrusion detection systems based on game theory
- IDS based on machine learning
- Decentralized intrusion detection
- Collaborative IDS (distributed)
- IDS based on reputation
- Intrusion detection system based on mobile agent
- Based on the statistical direction
- Anomaly intrusion detection
- An intrusion detection system that is hybrid
- IDS based on voting
- A cross-layer intrusion detection system
- Hierarchical intrusion detection systems
Our engineers have developed projects in all the above types of systems and we have improved upon the intrusion detection systems with the latest technologies. You can get in touch with us to know the ways that we used to enhance the IDS.
There are also issues in an intrusion detection system that arises out of the limitations in the system. Let us see about such limitations in detail below.
LIMITATIONS OF INTRUSION DETECTION
There are some limitations associated with intrusion detection systems that can be overcome by quality research. We guide you in rectifying such demerits in formulating intrusion detection thesis. The following are the challenges in intrusion detection system.
- Simulation in real-time
- Very few IDs designed in the past ten years have incorporated simulated datasets that are generated in real life
- Flaws are demonstrated in the IDs development
- Its limited capacity restricts its use to meet the demands of emerging needs
- Datasets for special purposes
- The datasets are limited for meeting some special purpose demands
- IoT datasets and SCADA are some examples of such special datasets
- Dataset outlook
- Methods of generation of the dataset have to be changed to cope with advancements in networking technologies
- Software-defined network or SDN, blockchain, big data, and network function virtualization or NFV have to be covered using datasets
- The generation of the dataset has to be in line with the recent trends
- Low Attacks Coverage
- Approximately 40% of known attacks are concentrated in public datasets in which does not suit in real-time.
Talk to our experts regarding how we nullified these defects. As we rendered research support to a lot of projects on intrusion detection systems, we can surely take you through the best path for the successful completion of your research. You should have a complete idea of many aspects of the intrusion detection system to write the best intrusion detection thesis. We are giving you all the essential details for your research which you can use to write your thesis. Now let us see in detail the possible intrusions
WHAT ARE THE INTRUSIONS?
The intrusions or interruptions that are possible in a network are listed below.
- Physical layer
- Perception systems (LIDAR and camera)
- Spooling
- Replay
- Jamming
- Blinding
- Tire–pressure monitoring systems or TPMS
- Tacking
- Spoofing
- Perception systems (LIDAR and camera)
- Application layer
- Bluetooth
- OBD port
- Frame sniffing
- Attacks due to replay
- Denial of service attack
- Frame falsifying
- Frame injecting
- CAN bus interface
- Replay attack
- Frame sniffing
- Wi-Fi
- Control system intrusion
- Remote access (wireless)
- Datalink layer
- CAN physical layer
- Denial-of-service attack
- OBD port
- Bluetooth
- Cellular Network
- Failure of the system
- CAN physical layer
The objective of the system of intrusion detection has to be to get rid of these intrusions and enhance the efficiency of the network. Our experts have come up with many innovations to solve the intrusion issues.
Get in touch with us and find out the successful intrusion detection systems that we modeled. We are ready to provide you with technical support to bring your creative ideas into intrusion detection thesis topics. Now let us have the ideas on different methods used in detecting intrusions.
INTRUSION DETECTION METHODS
The methods to detect intrusions in CRN systems are primarily based on different network parameters and functioning. The following are parameters involved in the intrusion detection process.
- Based on monitoring parameter (message level)
- Frequency-based
- Remote frame
- Statistical and white list based
- Based on machine learning (functional level)
- ID sequence and behavior analysis based
- HMM, TCMA, and decision tree-based
- Based on fingerprint (bus level)
- Clock based
- Measurement of voltage
- Based on intrusion theory (data – flow level)
- Hamming distance-based
- Analysis of entropy
Based on the above types, there are certain processes performed by the network to ensure efficient detection of intrusion. The following are the processes involved in methods of detecting intrusions
- Classification (category is predicted based on particular dataset)
- Ensemble (predictions of the classifiers are combined to form a single decision based on total weighted vote)
- Reinforcement learning (from the previous experiences the current action is determined)
- Optimization (the optimal solution is obtained from a set of iterative solutions)
- Regression (a continuous numeric value is predicted)
- Clustering (data sets are grouped into meaningful clusters)
- System of tools (if-then rules are taken up for classification)
We have our technical team who are highly skilled and updated about every method of advancement being developed to enhance the quality of intrusion detection techniques. Let us see about some of those techniques in intrusion detection below.
TECHNIQUES USED IN INTRUSION DETECTION THESIS
For the intrusion detection system to function correctly, the methods of feature selection and data mining have to happen efficiently. Let us see about the techniques involved in the below.
- Extraction and selection of features
- Using wrapper for feature selection
- FVBRM or Feature Vaslys based reduction method
- CSE or Consistency Subset Eval
- BFS or Best First Search
- SFS or Sequential Forward Selection
- RS or Rank Search
- IWD or Intelligent Water Drops
- GA or Genetic algorithm
- Filter for feature selection
- Chi-square
- GR or Gain Ratio
- KFDA or Kernel Fisher Discriminant Analysis
- CAE or Correlation Attribute Evaluator
- BPR or Borda Preference Rule
- IG or Information Gain
- Relief – F
- CB or Correlation Based
- FSE or Filtered Subset Eval
- Extraction of feature
- PCA or Principle Component Analysis
- Using wrapper for feature selection
- Data mining
- Regression
- RT or Regression Trees
- Optimization
- GA or Genetic Algorithm
- LP or Linear Programming
- Reinforcement learning
- LA or Learning Automata
- Classification
- K star
- K – NN or K-Nearest Neighbors
- SVM or Support Vector Machine
- ANN or Artificial Neural Network
- BN or Bayesian Networks
- DT or Decision Tree
- Ensembles
- AdaBoost
- Clustering
- K – means
- HC or Hierarchical clustering
- EM or Expectation Maximization
- Rule system
- Fuzzy
- AR or association rule
- OneR
- CR or Conjunctive Rule
- RR or Ripper Rule
- Regression
Our technical team will guide you on all aspects of these processes. We will provide you with all the necessary details to use and implement the above methods. Our team sets important targets and helps you achieve them proficiently.
You will be provided with deep insights into all sub-fields of your area of interest. We also provide you access to an enormous amount of reliable research information so that you can understand anything that is needed for your research. Now let us see about the performance metrics used for the evaluation of intrusion detection methods.
INTRUSION DETECTION PERFORMANCE METRICS
The intrusion detection systems can be evaluated on the following parameters. From the information that is extracted, you can make the following measurements on it.
- CPU Utilization
- Usage of processor
- CPU usage for a particular IDS task
- TRT or Training Time
- Time consumed for building and training a model for classification of IDS task
- CT or Computational Time
- Worst–case running time or execution time
- It is also called execution time or computational complexity
- It is the time taken for completion of particular tasks for classification of actions (into malicious or normal)
- EC or Energy Consumption
- It is also called power consumption
- Extra energy requirement for performing particular IDS tasks
- TST or Testing Time
- Classification of IDS actions into threatening or normal actions
Based on the above metrics the performance of the intrusion detection systems can be evaluated effectively. You can improve upon the IDS that you designed based on the answers that you get from the metrics mentioned above. Our team of technical experts can guide you based on this objective.
We have a special team of writers who will help you write the best thesis for your research project. We completely guide you for assignment writing, intrusion detection thesis and dissertation writing, and paper publication too. Now we will give you some ideas on how to write a good thesis.
HOW TO WRITE A QUALITY THESIS?
You must remember some points to write the best thesis. Out of the huge expertise that we gained in writing a thesis, our writers have come up with the following important points.
- The topic has to be treated in a straightforward and competent manner
- Collect a large amount of material on your topic of research to have a good hold on the field
- The data sources have to be utilized competently. This can give you better acquaintance with fundamental sources and present research
- As the thesis is the symbol of complete idea on the research you should represent all the subject matter in it
- The thesis must objective centric and the research question that you have chosen should be sustained throughout your thesis
Talk to our writers and research experts regarding the intrusion detection thesis. Our 24/7 customer support facility is highly equipped to guide you in the right way all the time. So connect with us for any kind of research support.
Are you collecting all the essential points for writing your thesis? Then refer to the following section which is going to be of great use to you.
How to write the thesis?
- Objectives and aims
- The central idea, theme, and theory that is investigated in your research have to be represented
- Background
- The background of the thesis or dissertation has to discussed
- The area of focus for the reader has to be highlighted
- Research Methodology
- The methodologies used in your research for generating the results have to explain well
- Results / Empirical Study
- The result of your findings have to be listed down
- Conclusions
- The central points for conclusion have to be arrived at while reading your complete research work
- Recommendations
- Mention the solutions very precisely that you suggest based on your research
- The best possible solutions to your research questions must be addressed in detail
The above points are the different sections in a thesis and we have also mentioned to you the importance of each section. You should remember these aspects while writing your intrusion detection thesis. You can approach us at any time to get your doubts on both writing and technical aspects resolved.