The process of creating a dissertation based on the network security field is a challenging as well as rewarding task. phdservices.org is the leading company who provides elite network security dissertation services on all areas. Performance Evaluation are aided by us for any types of concepts you come up with. All types of Simulation tools are worked by us we have completed more than 7000+ projects, work with us to experience the quality of our service. Below is a formatted procedure that we give you for this work, along with its various possible network security dissertation topics, methods and anticipated results clearly:
Potential Dissertation Topics
- Evaluating the Security of Next-Generation Wireless Communication Protocols
- Develop improvements or novel safety frameworks by researching the protection systems of evolving wireless protocols like 5G or Wi-Fi 6E including its susceptibilities.
- Machine Learning Approaches for Network Intrusion Detection
- By concentrating on minimizing false positives and adjusting to emerging threat figures, design and validate machine learning frameworks which can identify new network intrusions in a precise manner.
- Blockchain as a Solution for Secure Network Management
- For promoting protective interactions or assuring the morality of network configuration, discover the application of blockchain technique in handling network access controls.
- Impact of Quantum Computing on Network Encryption Methods
- Design quantum-resistible cryptographic measures through observing the possible attacks that are expressed by quantum computing to recent encoding regulations which are utilized in network security.
- Automated Threat Hunting in Large-scale Networks
- To detect and reduce the advanced persistent threats (APTs) practically throughout extensive networks, develop an automatic attack hunting model which manipulates artificial intelligence.
Methodology
- Literature Review: Based on the selected topic, carry-out an extensive survey of previous related exploration techniques and case studies. From this you can explain the requirements of your investigation and detect spaces in the latest insights.
- Experimental Design/Development: This might include incorporating a new safety model, constructing a framework or software tool and developing practical tests to experiment with particular assumptions according to your topic.
- Data Collection and Analysis: From simulations, real-time network analyses and practical tests, you should gather data. By implementing machine learning approaches, qualitative analysis methods and statistical techniques, observe the data properly.
- Assessment: This can include the process of assessing your findings in a controlled platform and contrasting them with previous frameworks. The performance, feasibility and robustness of your developed results or models should be evaluated.
Expected Outcomes
- New Knowledge: Whether by using practical data, the creation of novel technologies and devices or the conceptual frameworks, your dissertation must dedicate novel knowledge into network security difficulties.
- Practical Solutions: It can involve novel agreement experiences, software tools and safety protocols. Particularly to the previous network security experiences, you can develop realistic measures or improvements.
- Future Research Directions: By developing unique queries or problems that the upcoming work can tackle, find-out fields in which additional investigation is required.
Finalizing Your Dissertation
- Discussion and Conclusion: Describing their effects for network security experience and concept, integrate your results. Along with the real-time importance of your study and its challenges, define your conclusions explicitly.
- References: By following the suitable citation format, attach an extensive list of all the literary projects that are referenced to in your dissertation.
- Appendices: It is essential to offer additional resources like program scripts, elaborated data tables and extra practical findings to assist your exploration.
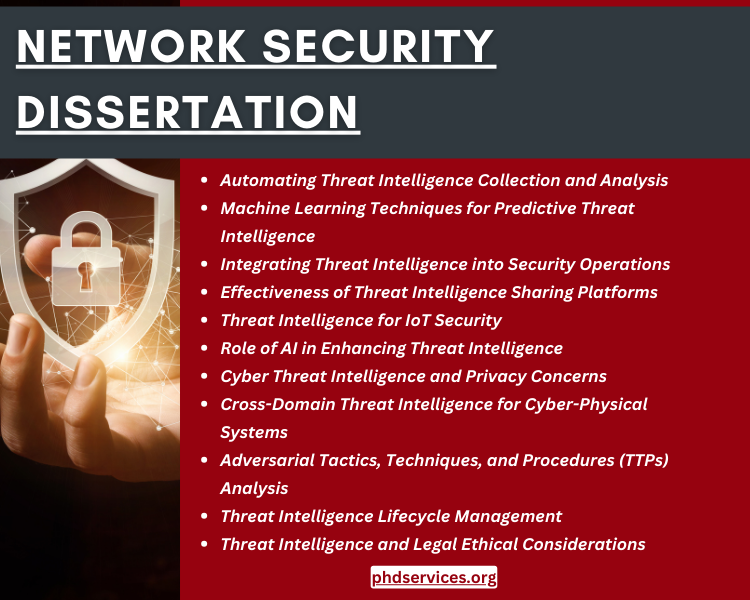
I am looking for dissertation topics on Threat Intelligence in information security any idea on some interesting topics
In information security, the area of Threat Intelligence is an excellent choice for choosing a dissertation topic which aligns with various latest technologies. We offer you a list of many threat intelligence-oriented dissertation topics which interest you and dedicate to the field specifically:
- Automating Threat Intelligence Collection and Analysis
- For gathering, executing and observing threat intelligence from different sources, discover the creation of automatic mechanisms. To increase the performance and the acceleration of attack identification and reaction, it also contains the dark web.
- Machine Learning Techniques for Predictive Threat Intelligence
- It is aiming at detecting the evolving attack vectors and sensitive goals and, depending on previous risk data, research the application of machine learning methods to forecast upcoming cyber threats.
- Integrating Threat Intelligence into Security Operations
- Along with the effect on correctness and incident response times, determine the difficulties and best experiences for combining threat intelligence into security operations centers (SOCs).
- Evaluating the Effectiveness of Threat Intelligence Sharing Platforms
- By targeting the hurdles to efficient distribution among associations and possible enhancements, observe the performance of previous threat intelligence sharing environments and models like STIX/AXII.
- Threat Intelligence for IoT Security
- For solving the specific issues like scalability, material constraint and device diversity, it targets creating unique threat intelligence methods for the Internet of Things (IoT) platform.
- The Role of Artificial Intelligence in Enhancing Threat Intelligence
- In forecasting attacker activities, automating decision-making and finding difficult figures specifically, discover how the threat intelligence task can be improved by artificial intelligence (AI).
- Cyber Threat Intelligence and Privacy Concerns
- Particularly in terms of private data gathering, research the confidentiality effects of cyber threat intelligence behavior and to equal efficient threat intelligence with confidentiality security, develop techniques regarding this.
- Cross-Domain Threat Intelligence for Cyber-Physical Systems
- Especially for commercial control systems and challenging architecture, investigate the advancement of multifaceted threat intelligence methods which include cyber as well as actual safety features.
- Adversarial Tactics, Techniques, and Procedures (TTPs) Analysis
- Focusing on constructing frameworks which can forecast threat ideas and notify defensive solutions and organizing a deep observation of adversarial TTPs with the help of threat intelligence data.
- Open Source Intelligence (OSINT) for Threat Intelligence
- To assist cybersecurity attempts, it targets methods for gathering and testing OSINT data robustly through analyzing the duty of OSINT in threat intelligence.
- Threat Intelligence Lifecycle Management
- From the process of collection and observation to distribution and functionalization, developing an extensive model for handling the lifecycle of threat intelligence for scaling its efficiency, it also has some metrics.
- Threat Intelligence and Legal Ethical Considerations
- Along with the problems that are relevant to consent, world-wide cooperation and data ownership, discover the valid and moral concerns around the application of threat intelligence and collection.
- Developing a Unified Threat Intelligence Platform
- For offering unauthorized knowledge for various shareholders, create and model an integrated threat intelligence setting which standardizes, observes and aggregates intelligence from dispersed sources.
Network Security Dissertation Topics & Ideas
Discover some of the Network Security Dissertation Topics & Ideas that we shared below, we come up individual topic and ideas that attract the readers.
- Determination of Security Index for Linear Cyber-Physical Systems Subject to Malicious Cyber Attacks
- Artificial Intelligence based Cyber Security Threats Identification in Financial Institutions Using Machine Learning Approach
- Reliability Assessment of Distribution Network Considering Cyber Attacks
- A Pragmatic Analysis of Pre- and Post-Quantum Cyber Security Scenarios
- Navigating the Cyber-Security Risks and Economics of System-of-Systems
- Towards resilient critical infrastructures: Application of Type-2 Fuzzy Logic in embedded network security cyber sensor
- Global Case Studies, Domains and Used Methodologies Concerning Cyber Security in Online banking: A Review
- Smart Cities: Emerging technologies and Potential solutions to the Cyber security threads
- Unlocking user-centered design methods for building cyber security visualizations
- Concept and Research Framework for Coordinated Situation Awareness and Active Defense of Cyber-physical Power Systems Against Cyber-attacks
- Necessity and Role of Blockchain Technology in the Domain of Cyber Security and Data Science
- Black Box Attacks on Explainable Artificial Intelligence(XAI) methods in Cyber Security
- A Robust Stackelberg Game for Cyber-Security Investment in Networked Control Systems
- Compensation for Voltage Disruption in a Smart Grid during Cyber–Attack
- Impact of DER integration on the cyber security of SCADA systems — The Medium Voltage regulation case study
- Cyber security for younger demographics: A graphic based authentication and authorisation framework
- Routing the Cyber-Attack Path with the Bayesian Network Deducing Approach
- Towards a Framework for the Extension and Visualisation of Cyber Security Requirements in Modelling Languages
- A Cyber-Physical Resilience-Based Survivability Metric against Topological Cyber attacks
- Cyber security in production networks — An empirical study about the current status


















