Network security is a significant approach that is particularly formulated to secure data privacy and morality from vulnerable attacks or threats. Original ideas with innovative topic suggestions on network security will be shared for scholars. Consult with us today we will guide you under all circumstances with best solution. Coding and simulation is also assisted by our developers. The following are numerous modern and current topics that are appropriate to conduct Phd exploration in the area of network security:
- Advanced Persistent Threat (APT) Detection and Response Mechanisms
- By considering methods that have an ability to find long-lasting, secretive intrusion activities of intricate assaulters, investigate new techniques in order to identify and reduce APTs.
- AI and Machine Learning for Predictive Network Security
- In terms of the investigation of network traffic patterns, abnormality identification, and user activities, forecast and prevent network safety hazards effectively by exploring the application of machine learning methods and artificial intelligence.
- Quantum Cryptography and Post-Quantum Network Security
- On modern network encryption techniques, examine the quantum computing influence. To safeguard upcoming network interactions, create quantum-resistant cryptographic protocols.
- Blockchain-based Security Protocols for Decentralized Networks
- With the intention of improving privacy, morality, and accessibility of data in decentralized networks such as peer-to-peer networks and IoT environments, the blockchain-related safety protocols have to be modeled and assessed.
- Zero Trust Network Architectures
- By concentrating on limited privilege enforcement and protective access handling, explore the Zero Trust framework’s efficiency and application problems in different industrial backgrounds.
- Privacy-preserving Network Protocols
- Especially for the purpose of messaging, web browsing, and online transactions, create network protocols by including various methods such as zero-knowledge proofs and onion routing and these are capable of assuring secrecy and confidentiality for users.
- Cyber-Physical System (CPS) Security
- In cyber-physical frameworks like self-driving vehicles or industrial control systems, investigate the safety limitations. In opposition to assaults that can have physical impacts, securing these frameworks are the major goal.
- Network Security for Edge Computing
- The particular safety issues that are caused by edge computing frameworks have to be considered. To carry out safer data processing at the network edge nearer to IoT sensors and devices, suggest strategies.
- Secure Software-Defined Networking (SDN)
- Relevant to SDN platforms, the safety risks must be explored. For SDN controllers, create powerful safety technologies, and among network devices and controllers, build interaction channels.
- Adversarial Attacks and Defenses in Network Security
- Contrary to network safety systems that specifically utilize AI, the basis of adversarial assaults has to be explored. To secure from these assaults, create security policies.
- Security Implications of 5G Networks
- In the 5G network deployment, the safety impacts such as the possible risks that are posed by novel protocols and mechanisms must be examined. For protecting the 5G framework, suggest effective policies.
- Cross-Domain Security Policy Enforcement
- For assuring coherent safety measures in multi-tenant platforms, methodologies have to be explored to develop and implement safety strategies that encompass various industrial settings and network fields.
- IoT Security and Privacy Frameworks
- Focus on solving scalability issues, device heterogeneity, and problems related to data confidentiality in Internet of Things (IoT) by creating extensive confidentiality and safety models.
- Automated Penetration Testing and Network Hardening
- In penetration testing, the benefits of automatic activities to meticulously identify and minimize networks risk must be explored. Through the consistent evaluation, the safety measures of networks could be improved.
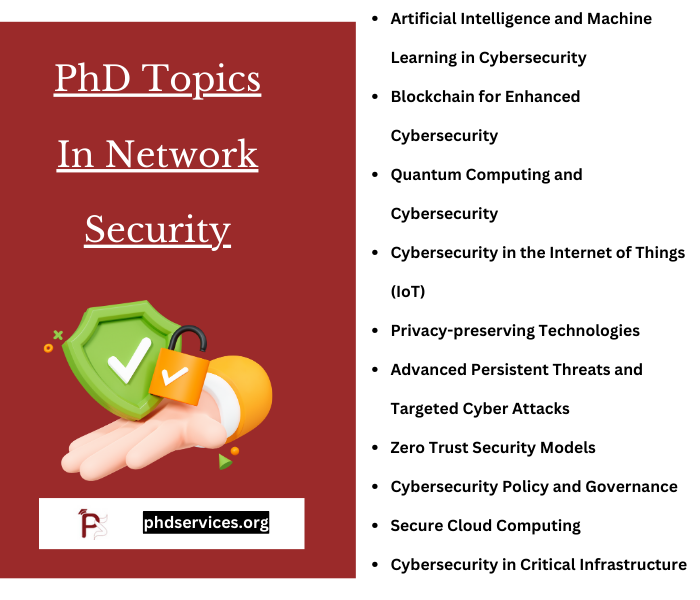
What are the best research topics in cyber security?
In this digital era, cybersecurity is considered as an important aspect to protect all individual information from illicit access and vulnerable threats. Relevant to cybersecurity, we suggest a few effective and latest research topics that could inspire you to carry out an intriguing exploration:
- Artificial Intelligence and Machine Learning in Cybersecurity
- Explore in what way threat identification, safety analytics, and response automation can be improved by AI and ML. The possible vulnerabilities that are caused by these mechanisms, like AI-based cyber assaults have to be investigated.
- Advanced Persistent Threats (APTs) and Targeted Cyber Attacks
- In order to identify, reduce, and react to APTs along with interpreting assaulter tactics, techniques, and procedures (TTPs), explore policies.
- Blockchain for Enhanced Cybersecurity
- Over cryptocurrencies, the applications of blockchain mechanisms such as strengthening identity management, reinforcing morality of data in distributed frameworks, and protecting IoT networks must be examined.
- Quantum Computing and Cybersecurity
- On the latest encryption principles, explore the quantum computing impacts. To protect upcoming interactions, the progression of quantum-resistant cryptographic methods has to be studied.
- Cybersecurity in the Internet of Things (IoT)
- By concentrating on creating scalable safety models and protocols to secure from IoT-based hazards, solve the particular limitations in protecting IoT networks and devices.
- Privacy-preserving Technologies
- Specifically in terms of social network and big data, secure user confidentiality by exploring various mechanisms like homomorphic encryption, differential privacy, and secure multi-party computation.
- Zero Trust Security Models
- In assuring protective access in gradually perimeter-less platforms and securing from insider hazards, the standards and applications issues of Zero Trust frameworks must be explored.
- Cybersecurity Policy and Governance
- At national and international range, the efficacy of the latest cybersecurity architectures, strategies, and governance prototypes must be examined. To improve worldwide cybersecurity collaboration, suggest novel techniques or enhancements.
- Ethical Hacking and Penetration Testing
- For penetration testing, consider the creation of novel ethical hacking approaches, techniques, and tools. This idea is particularly for finding and minimizing risks in different frameworks.
- Secure Cloud Computing
- In cloud computing platforms, the safety issues related to data confidentiality, safer cloud migration policies, and multi-tenancy vulnerabilities must be investigated.
- Digital Forensics and Incident Response
- For exploring cybercrimes and violations, the developments in digital forensics tools and methods have to be studied. In addition to that, examine greater approaches for efficient phenomenon response.
- Social Engineering Attacks and Human Factors in Cybersecurity
- The psychology in social engineering-based assaults must be investigated. To aware and secure users against these highly complicated hazards, study effective techniques.
- Emerging Threats in Cyber-Physical Systems
- The cybersecurity impacts of cyber-physical frameworks like smart grids, industrial control systems, and self-driving vehicles have to be examined.
- Regulatory Compliance and Cybersecurity
- On industrial cybersecurity approaches, the influence of regulatory models such as CCPA, GDPR, or HIPAA must be analyzed. In preserving regulatory adherence, study the major problems.
- Cybersecurity in Critical Infrastructure
- In opposition to cyber hazards, the security policies and risks for important infrastructure areas like finance, energy, and healthcare should be explored.
PhD Ideas in Network Security
A few list of PhD Ideas in Network Security that we assisted as customized service for scholars are listed below, read our ideas if you are looking for original work then phdservices.org will be your best research partner, all your work will be done right from scratch. Stay connected with us we will create best thesis work that attracts the readers.
- An Ontology to Promote Interoperability between Cyber-physical Security Systems in Critical Infrastructures
- A Bayesian Algorithm to Enhance the Resilience of WAMS Applications Against Cyber Attacks
- Game theoretic framework for cyber-physical system security incorporating bounded rationality
- A New Design for Protecting Cyber-Attacks and Harmful Threats in IoT Communication Network with Efficient Deep Learning-Based Detection System
- Adding a Third Dimension to BPMN as a Means of Representing Cyber Security Requirements
- Cyber Security Challenges in Distributed Energy Resources for Smart Cities
- On the Security of Cyber-Physical Systems Against Stochastic Cyber-Attacks Models
- Resilient Distributed Optimization Algorithm for Economic Dispatch Against Cyber-Attacks in Smart Grid
- Cyber Security Social Engineers An Extensible Teaching Tool for Social Engineering Education and Awareness
- Enhancing Smart Grid Cyber-Security Using A Fuzzy Adaptive Autonomy Expert System
- Making DNS Servers Resistant to Cyber Attacks: An Empirical Study on Formal Methods and Performance
- Cyber-Attack Detection and Cyber-Security Enhancement in Smart DC-Microgrid Based on Blockchain Technology and Hilbert Huang Transform
- Enabling intelligent cities through cyber security of building information and building systems
- Critical Information Framework against Cyber-Attacks using Artificial Intelligence and Big Data Analytics
- Ranking Cyber Attack Vulnerability of Nodes in Power Transmission Network
- Cyber-physical security for Low-Voltage Smart Grids HAN security within Smart Grids
- Cyber security issues in conductor temperature and meteorological measurement based DLR system
- Game-Theoretic Model for Optimal Cyber-Attack Defensive Decision-Making in Cyber-Physical Power Systems
- A Detailed Investigation of Implementation of Internet of Things (IOT) in Cyber Security in Healthcare Sector
- General Requirements of a Hybrid-Modeling Framework for Cyber Security


















