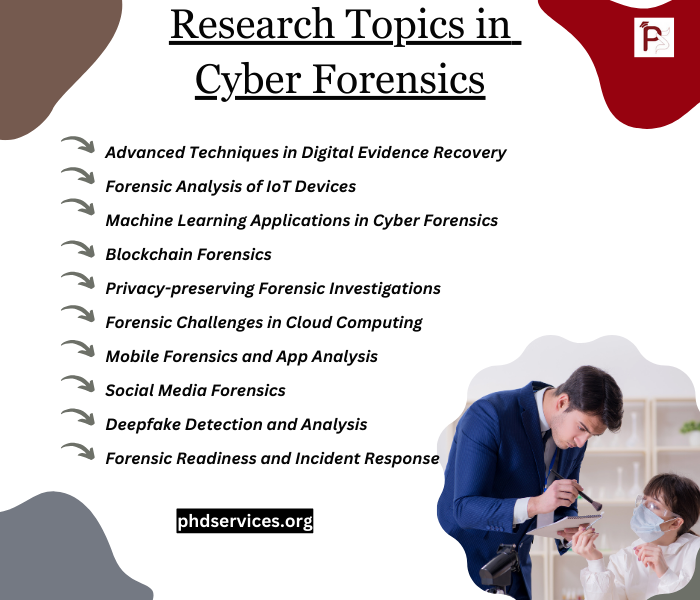
Cyber forensics is an interesting domain that employs various exploration methods for the purpose of finding, and gathering digital proof. Latest advancements and trending methodologies pave a vital part to carry on Cyber forensics research work. On the basis of this domain, we list out various research topics that are more related to the issues confronted by the experts in this discipline as well as modern:
- Advanced Techniques in Digital Evidence Recovery
- Aim: In order to retrieve data from highly complicated online platforms like cloud storage and encrypted devices, create novel tools and techniques.
- Forensic Analysis of IoT Devices
- Aim: For forensic analysis of Internet of Things (IoT) devices, examine approaches. This analysis process might include interaction protocols, the limitation of disjointed environments, and specific data patterns.
- Machine Learning Applications in Cyber Forensics
- Aim: To automate factors of the online forensic operations like detection of patterns in a wide range of datasets or categorization of malware attacks, employ methods of machine learning.
- Blockchain Forensics
- Aim: In terms of confidentiality violations, illicit activities, and cryptocurrency hazards, examine smart contracts and blockchain transactions by exploring techniques.
- Privacy-preserving Forensic Investigations
- Aim: Through the utilization of various approaches such as anonymization or differential privacy, create forensic methodologies. While working with personal information, these methodologies obey the confidentiality of the user.
- Forensic Challenges in Cloud Computing
- Aim: In carrying out forensic analysis in cloud platforms, solve any potential challenges such as cloud provider dependencies, multi-tenancy, and data locality problems.
- Mobile Forensics and App Analysis
- Aim: By focusing on the app encryption, variety of operating systems, and cloud incorporation, increase the abilities of forensic, specifically to examine data from mobile devices and applications in an efficient manner.
- Social Media Forensics
- Aim: For gathering and examining data from social media environments, create methods and tools. In analysis relevant to digital fraud, radicalization, and cyberbullying, this idea is very helpful.
- Deepfake Detection and Analysis
- Aim: Identify and study deepfake images and video feeds that could cause novel limitations for validating the reliability of digital proof. For that, explore efficient techniques.
- Forensic Readiness and Incident Response
- Aim: Within the context of the firm’s incident response strategy, improve its forensic alertness by analyzing policies. This topic assures that digital proof is maintained and gathered following a safety phenomenon in an effective way.
- Network Forensics and Anomaly Detection
- Aim: Find illicit access and malicious events by encompassing the utilization of anomaly identification framework. To carry out this plan, examine network traffic by improving methods.
- Legal and Ethical Issues in Digital Forensics
- Aim: By considering various problems based on cross-border data access, search permissions, and the eligibility of digital proof in court, the legal and moral impacts of online forensic approaches have to be investigated.
- Digital Forensics in the Dark Web
- Aim: Illicit operations in the dark web, such as selling of stolen information, cyber-arms, and the drug trading must be explored by utilizing techniques along the way of anonymity tools.
- Multimedia Forensics
- Aim: For the objective of analysis, retrieve metadata, or identify copyright violation or manipulation by examining multimedia data like audio, video feeds, or images through the use of robust methods.
What is digital forensics in network security research?
Digital forensic is an important area that concentrates on various processes like proof finding, gathering, maintaining, analyzing, depicting and so on. In the process of network security, digital forensics plays a major role. Below, we describe its major functionalities and procedures:
- Identification: The processes of finding and deciding the range of a safety violation or event are included in this phase. Detecting the impacted framework, the degree of the data that are used illegally or harmed, and the type of the assault might be encompassed.
- Collection: This step represents the collection of digital proof. Various processes such as gathering of records from routers, servers, firewalls, and other network devices, protection of any unstable information that might be missed while power loss or reboot incidents, and seizing of actual time traffic through the utilization of network sniffing tools could be included in a network.
- Preservation: Note that the protected data should not be modified from its actual format. It should conserve its morality. Development of actual bit-for-bit copies that are forensic images of digital proof and maintenance of protection chain that specifically reports by whom the proofs are managed and how, from the process of gathering and depiction could be included in this phase.
- Analysis: To know about the incident, the reason behind that incident, and the responsible aspects, analysts study the gathered proofs. Several processes could be encompassed in this step such as evaluating network traffic for the purpose of identifying abnormalities, monitoring activities of assaulters by investigating recorded files, and retrieving harmed, encrypted, or missed information through the use of different tools. The rebuilding of the phenomena that generated the safety incident is the major goal of this analysis process.
- Presentation: A document is prepared by arranging all the acquired discoveries from the analysis. It specifically encompasses the proofs, in what way the data gathering and analysis process was carried out, and the conclusions that are obtained from the analysis. This document must be depicted in an eligible way that is appropriate in legal procedures if required and should be interpretable to the non-expert participants like industrial management or legal communities.
- Incident Response and Mitigation: To minimize the effect of the latest violations and to impede same phenomena in the upcoming periods, the details that are acquired at the time of analysis process is most significant, especially for creating an efficient phenomenon response, even though not a phase of the forensic analysis.
Research Ideas in Cyber Forensics
Research Ideas in Cyber Forensics ideas are listed you can read our work and get your research customized according to your academic protocols. Our team of experts is prepared to address any inquiries you may have and assist you in navigating the process, enabling you to make well-informed choices regarding your academic journey.
- Cyber Attack Thread: A control-flow based approach to deconstruct and mitigate cyber threats
- Reconstruction of measurements in state estimation strategy against cyber-attacks for cyber physical systems
- Use of Machine Learning algorithms for designing efficient cyber security solutions
- Robustness of Asymmetric Cyber-Physical Power Systems Against Cyber Attacks
- Cyber Security Inference Based on a Two-Level Bayesian Network Framework
- Network Traffic Analysis for Real-Time Detection of Cyber Attacks
- A review on cyber security datasets for machine learning algorithms
- Digital Twin-Enhanced Methodology for Training Edge-Based Models for Cyber Security Applications
- Cyber Security Flood Attacks and Risk Assessment for Internet of Things (IoT) Distributed Systems
- Systematic analysis of cyber-attacks on CPS-evaluating applicability of DFD-based approach
- Limitations of state estimation based cyber attack detection schemes in industrial control systems
- Data-Driven Approach for Detection of Physical Faults and Cyber Attacks in Manufacturing Motor Drives
- Post Pandemic Cyber Attacks Impacts and Countermeasures: A Systematic Review
- Identification of Spatio- Temporal Patterns in Cyber Security for Detecting the Signature Identity of Hacker
- Identification of Spatio-Temporal Patterns in Cyber Security for Detecting the Signature Identity of Hacker
- Review of Cyber-Physical Attacks and Counter Defense Mechanisms for Advanced Metering Infrastructure in Smart Grid
- Optimal Adaptive Coordinated Cyber-Attacks on Power Grids using ∊-Greedy Method
- Intrusion Detection and Prevention Approach in Wlan Using Cyber Security
- On the Cyber Security of Lebanon: A Large Scale Empirical Study of Critical Vulnerabilities
- Application stress testing Achieving cyber security by testing cyber attacks


















