What is NS3?
NS3 is important to network simulators which help to simulate a wide range of networks and systems. To simulate a wide range of networks, there are different applications, protocols, and modules. This simulation is written with C++ Language and wrapped up with python. It helps in creating a variety of virtual nodes.
Network simulator 3 helps in creating a base for the technologies; it helps us in building applications.
Our experts have years of reputation in researching multiple topics. And our experts are working on this technology to give a broader view of information. They have massive sources and it’s reliable.
NS3 Key Features
Some NS3 key features would help to know the functions of the simulation. The functions help us in understanding NS3 deeply. The points are given below
- By callbacks, numerous trace points are enabled.
- Quarterly releases
- Trace output in ASCII, or Pcap format – Use exciting Pcap tools.
- Documentation of Doxygen
- Check-in procedure/ Formal review
- Flexible Event Scheduler is there with arbitrary parameter lists.
- Repository of Mercurial Code
- Using Existing Pcap tools like wireshark, output can be traced in ASCII or Pcap.
NS3 has many uses which can enrich the usage of network simulation. It can work with User Datagram Protocol which enables the transmission of data in a high-speed manner. Like this, there are many applications which are discussed below
Applications (traffic generators)
- Udp-client/server : Sends UDP packet w/ sequence number.
- Radvd : Advertisement for Router.
- Udp-echo : No sequence number sends UDP packet.
- Packet Sink : TCP connections or receives packets.
- Ping6, v4ping : Send ICMP ECHO request
- Onoff
- Alternating on-and-off periods, generates streams
- Highly parameterized
- If it is well arranged, it generates many types of traffic.
E.g. OnTime = 1 and OffTime = 0 means CBR
- Works with either UDP or TCP.
We should know that the NS3 packet contains the bundle of metadata, a list of tags, and a byte buffer.
NS3 PACKET
Each network contains the packet which is the list of tags, byte buffer, and metadata.
- Metadata : Serialized types of headers and trailers have been described.
- Enables packets to print themselves
- Optional – disabled by default
- Tags : Set of user-provided data structures, arbitrary.
- Buffer : Representation of headers and trailers in bit by bit.
Our experts are professionals in technology-based research, where it didn’t stop with only research but they have given the application for our easy understanding. The algorithms are pointed below.
Latest Algorithms in NS3
- BFTR Algorithm
We included the Best Effort Fault-Tolerant Routing (BFTR) algorithm to work on the authentication principle. By this shortest and feasible path, the Packet delivering ratio can be increased by statistics and DSR Flooding. End to End Packet delivery can be making sure even though there are attacks such as Fabrication, Dropping, Misrouting, Tampering, Corruption, and Replaying can be resolved by our academic projects.
- TIARA Algorithm
By the technique, Intrusion Resistant Ad hoc Routing Algorithm (TIARA), MANET communication is improved by our experts. To make the temper attack effect in the network, this algorithm is used. There are some following techniques which will be discussed below.
- FRAC Technique
To control the sequence of packets of source and destination node, the flow-based route access (FRAC) Technique is used. To describe an authorized flow of every intermediate node for the entire, the network route policy is retained. To detect and inform the detected path failure to the source node is performed by the FRAC technique. For transmission of data, another route is selected by the source node.
- Resource Allocation
Resource Depletion attacks happen by the collision of two attacker combinations and they cooperate through the direct link. We implement this resource allocation technique. To maintain resources we define a threshold value for all nodes. From other trusted nodes, we provide additional resources.
- Flow Monitoring
Flow Monitoring is performed by a flow status message of digital signature and routing function send it in springer papers. In the process of routing, there is source and destination node sequence number. Among multiple routes in source and destination, the source node selects the best one.
- Fast Authentication
To implement fast authentication of data packets, each packet in the network has its own path label at a particular secret location. This works on Packet Label Notation. Packet secret location is changed periodically to remove traffic analysis attacks.
Our experts have designed some topics in vehicular communication simulations with NS3. They are network devices, nodes, and mobility, their applications. Some of the topics are explained with examples below.
Vehicular Communication Simulation using NS3
- Applications
- ON and OFF (Generic) and ITS based applications
- Nodes and Mobility
- Moving elements (vehicles, pedestrians, other)
- Static elements (road side units, traffic lights, sensors in buildings).
- Network Devices
- Communication technologies (ad hoc, infrastructure) such as WiFi, WAVE, Wired P2P, and other.
- Network /Routing
- Routing protocols design for various networks such as MANET / VANET Simulator
WiMesh using NS3 Simulation
In NS3, Wimesh is a tool used for wireless mesh networks simulation and analysis. This tool automatically sets up and executes an NS3 simulation initiated from the network topology as returned by the selected channel assignment algorithm.
This software tool allows comparing and verifying the performances of the number of algorithms told in the literature to assign transmission rate, channel, NS3 5g and power to the radios of the network nodes.
RapidNet using NS3
RapidNet helps in developing a networking engine with the NS3 network simulator. A distributed recursive query language called Network Datalog (NDlog) is used in specifying Network protocols. A protocol specification in NDlog is compiled into NS3 code which is in C++ using the RapidNet compiler. In simulation mode, the NS3 application runs in the form of compiled code.
Here, NDlog is utilized as an actual implementation using the NS3 network emulator, so it provides a bridge between Testbed based experimentation and simulation.
In this NS3 simulation project, our experts have made in-depth research towards its advantages it can be helpful in solving the queries of wireless sensor networks.
NS3 simulation projects
- Tunnel comparison between Generic Routing Encapsulation (GRE) and IP Security.
The objective behind this project is to arrange a network with these two different Tunnel techniques and compare the network performance and security. Traffic Captures is sent using the two security techniques, GRE tunnel and IP sec/VPN will be monitored.
- Jperf-tool – measures network performance and show specific detail.
- Wireshark – captured information is analyzed during transmission.
IP sec is a standard security protocol solution and it provides security through data integrity, authentication, and encryption. GRE helps for packets encapsulation and creates a typology of virtual point-to-point connection by a logical hub-and-spoke.
- Dynamic Conflict-Free Transmission Scheduling for Sensor Network Queries (DCQS)
This scheduling is specifically designed in a wireless sensor network for query services, in contrast to the TDMA protocol built for the general-purpose workload. It has some unique features.
- Query performance through conflict-free transmission – Properties of wireless sensor networks.
- Performance- maximum achievable query rate.
- Handle overload through rate control.
NS3 Simulation has a wide range of applications in technology. Our experts have deep knowledge of this topic. Some project topics are designed to enrich your ideas for the research. They are given below.
NS3 Simulation Project Titles
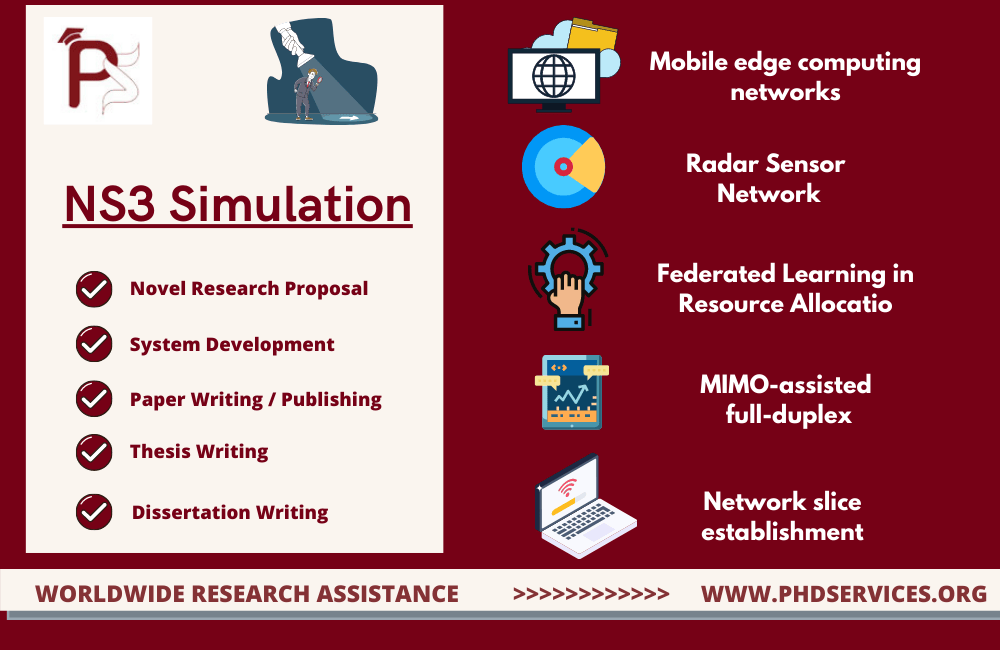
- Enabled Mobile edge computing networks – resource allocation in UAV and fairness-aware task scheduling.
- In Radar Sensor network, Quality of Service constrained – Resource allocation scheme for multiple target tracking.
- Latency constrained Wireless Federated Learning in Resource Allocation and Joint Device Scheduling.
- An intelligent approach for resource sharing and allocation in wireless MIMO-assisted full-duplex backscatter communication.
- Through deep learning, network slice establishment and dynamism in management are enhanced.
NS3 Simulation is the biggest topic, where the information given in this article is not a limit to this topic. Our experts will give information regarding this topic in a detailed manner. Experts give online guidance for this latest updated topic. For your queries, you can communicate with them at any time.


















